NextCloud memberOf
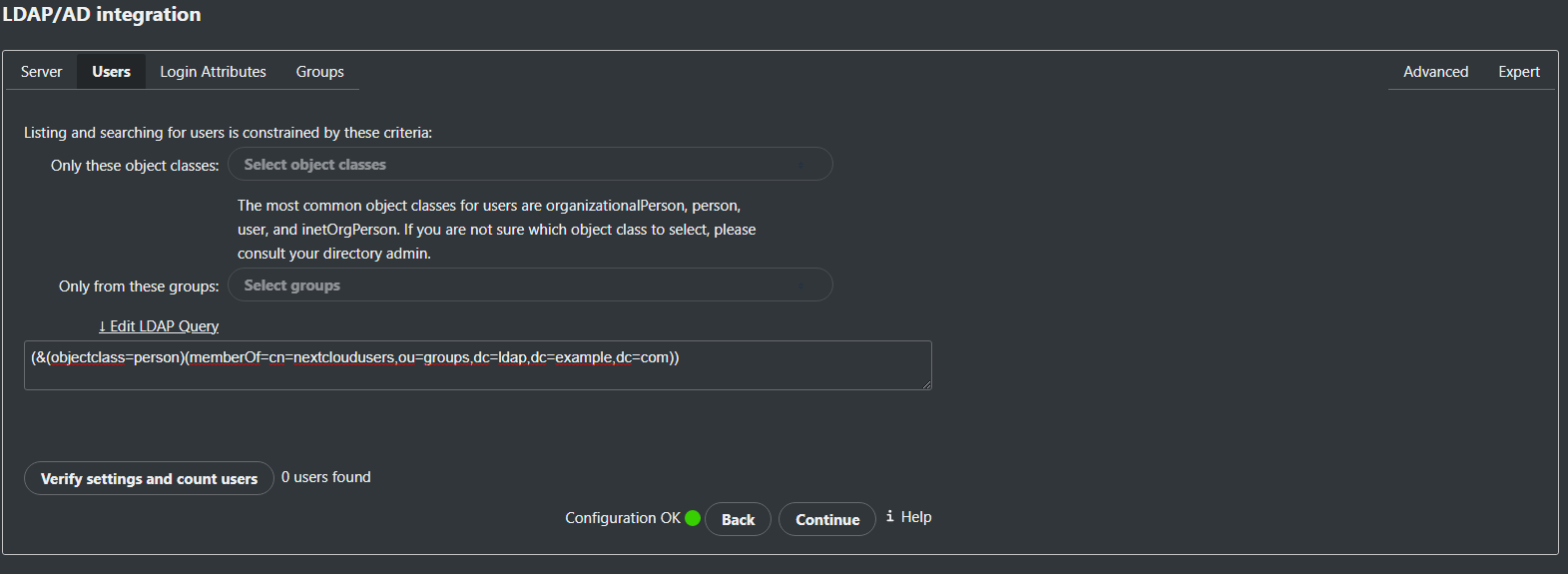
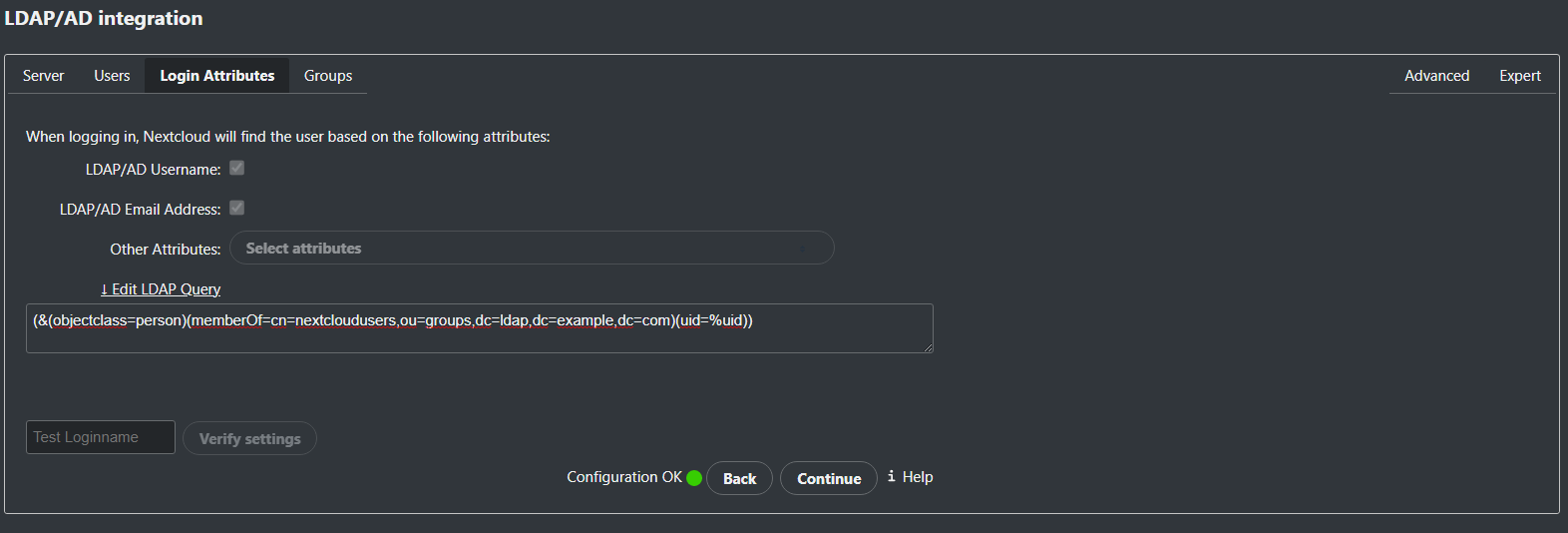
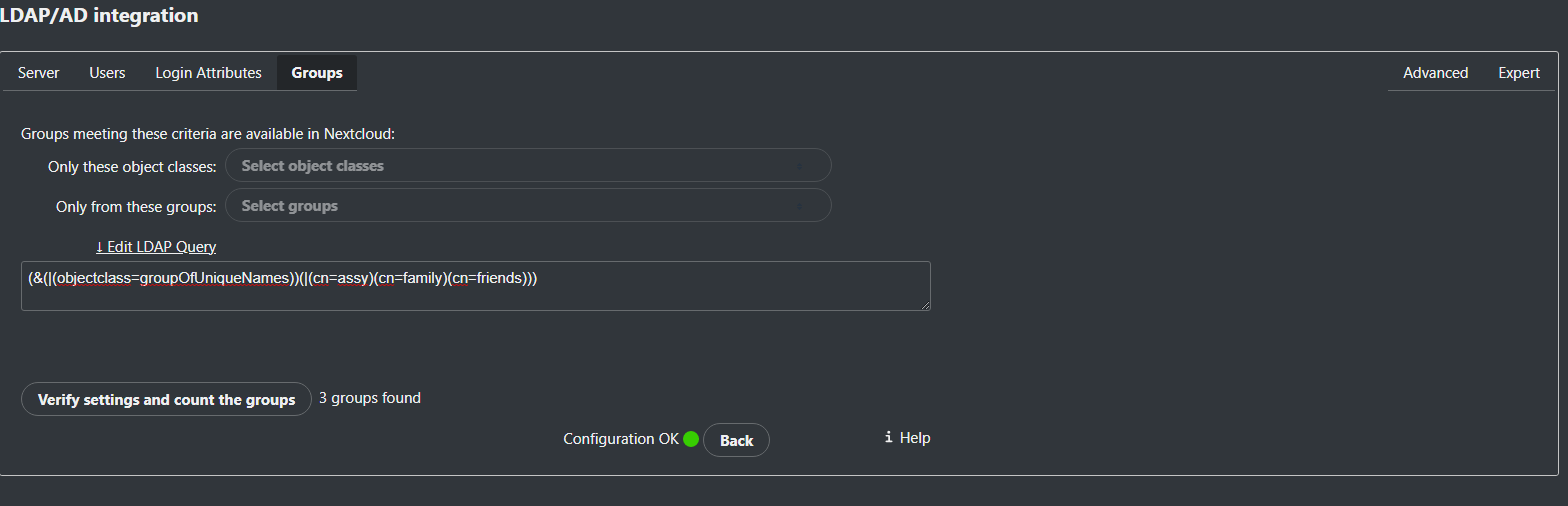
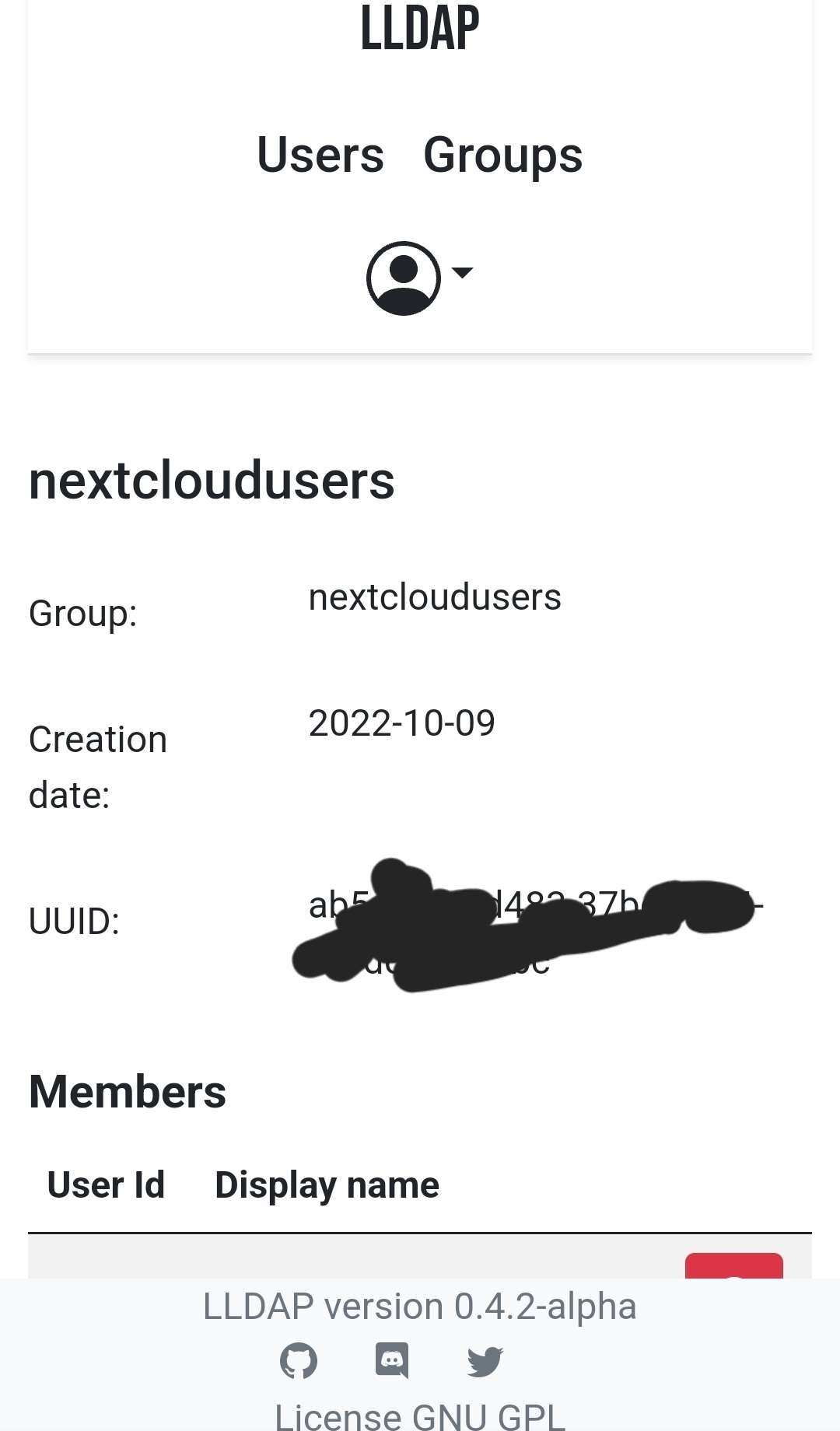
Hi, I pulled the new image and tried the filter again. It didn't work, gives 0 users and an error message in the lldap log compared to 0.4.1 that gives all objects. Maybe I am using the filter wrong? The filter I am using for only allowing members in the nextcloudusers group os the following;
(&(objectclass=person)(memberOf=cn=nextcloudusers,ou=groups,dc=ldap,dc=example,dc=com))
This gives me 0 results and an error message in the lldap log.
2022-10-19T17:07:15.540109083+00:00 DEBUG │ │ ┕━ get_groups_list [ 155µs | 0.02% / 0.12% ]
2022-10-19T17:07:15.540117183+00:00 DEBUG │ │ ┝━ [debug]: | ldap_filter: And([And([Equality("objectclass", "person"), Equality("memberOf", "cn=nextcloudusers,ou=groups,dc=ldap,dc=example,dc=com")]), Present("displayname")])
[debug]: | ldap_filter: And([And([Equality("objectclass", "person"), Equality("memberOf", "cn=nextcloudusers,ou=groups,dc=ldap,dc=example,dc=com")]), Present("displayname")])
2022-10-19T17:07:15.540122763+00:00 WARN │ │ ┝━ [warn]: Ignoring unknown group attribute ""memberof"" in filter.\n\
[warn]: Ignoring unknown group attribute ""memberof"" in filter.\n\
To disable this warning, add it to "ignored_group_attributes" in the config.
2022-10-19T17:07:15.540126703+00:00 DEBUG │ │ ┝━ [debug]: | parsed_filters: And([And([Not(And([])), Not(And([]))]), Not(And([]))])
[debug]: | parsed_filters: And([And([Not(And([])), Not(And([]))]), Not(And([]))])
2022-10-19T17:07:15.540127893+00:00 DEBUG │ │ ┕━ list_groups [ 131µs | 0.10% ]
2022-10-19T17:07:15.540132133+00:00 DEBUG │ │ ┝━ [debug]: | filters: Some(And([And([Not(And([])), Not(And([]))]), Not(And([]))]))
[debug]: | filters: Some(And([And([Not(And([])), Not(And([]))]), Not(And([]))]))
2022-10-19T17:07:15.540193852+00:00 DEBUG │ │ ┝━ [debug]: | query: SELECT "groups"."group_id", "display_name", "creation_date", "uuid", "user_id" FROM "groups" LEFT JOIN "memberships" ON "groups"."group_id" = "memberships"."group_id" WHERE ((NOT (?)) AND (NOT (?))) AND (NOT (?)) ORDER BY "display_name" ASC, "user_id" ASC
[debug]: | query: SELECT "groups"."group_id", "display_name", "creation_date", "uuid", "user_id" FROM "groups" LEFT JOIN "memberships" ON "groups"."group_id" = "memberships"."group_id" WHERE ((NOT (?)) AND (NOT (?))) AND (NOT (?)) ORDER BY "display_name" ASC, "user_id" ASC
2022-10-19T17:07:15.540303400+00:00 DEBUG │ │ ┕━ [debug]: | return: []
[debug]: | return: []
(&(objectclass=person)(memberOf=cn=nextcloudusers,ou=groups,dc=ldap,dc=example,dc=com))
This gives me 0 results and an error message in the lldap log.
2022-10-19T17:07:15.540109083+00:00 DEBUG │ │ ┕━ get_groups_list [ 155µs | 0.02% / 0.12% ]
2022-10-19T17:07:15.540117183+00:00 DEBUG │ │ ┝━
 [debug]: | ldap_filter: And([And([Equality("objectclass", "person"), Equality("memberOf", "cn=nextcloudusers,ou=groups,dc=ldap,dc=example,dc=com")]), Present("displayname")])
[debug]: | ldap_filter: And([And([Equality("objectclass", "person"), Equality("memberOf", "cn=nextcloudusers,ou=groups,dc=ldap,dc=example,dc=com")]), Present("displayname")])2022-10-19T17:07:15.540122763+00:00 WARN │ │ ┝━
 [warn]: Ignoring unknown group attribute ""memberof"" in filter.\n\
[warn]: Ignoring unknown group attribute ""memberof"" in filter.\n\To disable this warning, add it to "ignored_group_attributes" in the config.
2022-10-19T17:07:15.540126703+00:00 DEBUG │ │ ┝━
 [debug]: | parsed_filters: And([And([Not(And([])), Not(And([]))]), Not(And([]))])
[debug]: | parsed_filters: And([And([Not(And([])), Not(And([]))]), Not(And([]))])2022-10-19T17:07:15.540127893+00:00 DEBUG │ │ ┕━ list_groups [ 131µs | 0.10% ]
2022-10-19T17:07:15.540132133+00:00 DEBUG │ │ ┝━
 [debug]: | filters: Some(And([And([Not(And([])), Not(And([]))]), Not(And([]))]))
[debug]: | filters: Some(And([And([Not(And([])), Not(And([]))]), Not(And([]))]))2022-10-19T17:07:15.540193852+00:00 DEBUG │ │ ┝━
 [debug]: | query: SELECT "groups"."group_id", "display_name", "creation_date", "uuid", "user_id" FROM "groups" LEFT JOIN "memberships" ON "groups"."group_id" = "memberships"."group_id" WHERE ((NOT (?)) AND (NOT (?))) AND (NOT (?)) ORDER BY "display_name" ASC, "user_id" ASC
[debug]: | query: SELECT "groups"."group_id", "display_name", "creation_date", "uuid", "user_id" FROM "groups" LEFT JOIN "memberships" ON "groups"."group_id" = "memberships"."group_id" WHERE ((NOT (?)) AND (NOT (?))) AND (NOT (?)) ORDER BY "display_name" ASC, "user_id" ASC2022-10-19T17:07:15.540303400+00:00 DEBUG │ │ ┕━
 [debug]: | return: []
[debug]: | return: []